What is Voice Over Internet Protocol or (VoIP) technology?
It is ideal for business use as it replaces
landlines and reduces overall communication costs.
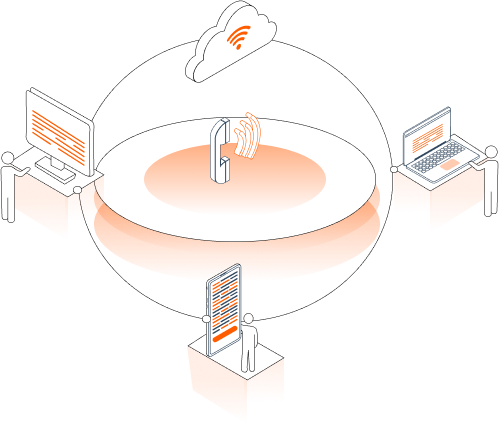
Voice Over Internet Protocol or (VoIP) technology allows users to make phone calls
over the internet. It is ideal for business use as it replaces landlines and reduces
overall communication costs. It also allows for integration with online IT systems
and external based-internet services, including video and teleconferencing.
Voice Over Internet Protocol or (VoIP) technology allows users to make phone calls
over the internet. It is ideal for business use as it replaces landlines and reduces
overall communication costs. It also allows for integration with online IT systems
and external based-internet services, including video and teleconferencing.
All these advantages make VoIP a great option, but it also comes with VoIP security
challenges. Because VoIP systems are internet-based, there is a risk of cyberattacks
and malicious breaches. Companies must ensure that their cloud-based phone system is
secure and resilient to VoIP security threats.
Voice Over IP (VoIP) security assessment is the manual checking of your VoIP or
cloud-based telephony systems. Microminder offers extensive VoIP security assessment
services to ensure that your systems are not vulnerable to attacks.
Many organisations cannot fully monitor all the potential VoIP security threats,
placing sensitive devices and networks at risk. Microminder can comprehensively
address and evaluate all VoIP infrastructure and identify all security loopholes in
your organisation’s voice and text network.
Read More +
Read Less -





























 310 reviews on
310 reviews on 




















