
Thank you
Our team of industry domain experts combined with our guaranteed SLAs, our world class technology .


Get Immediate Help
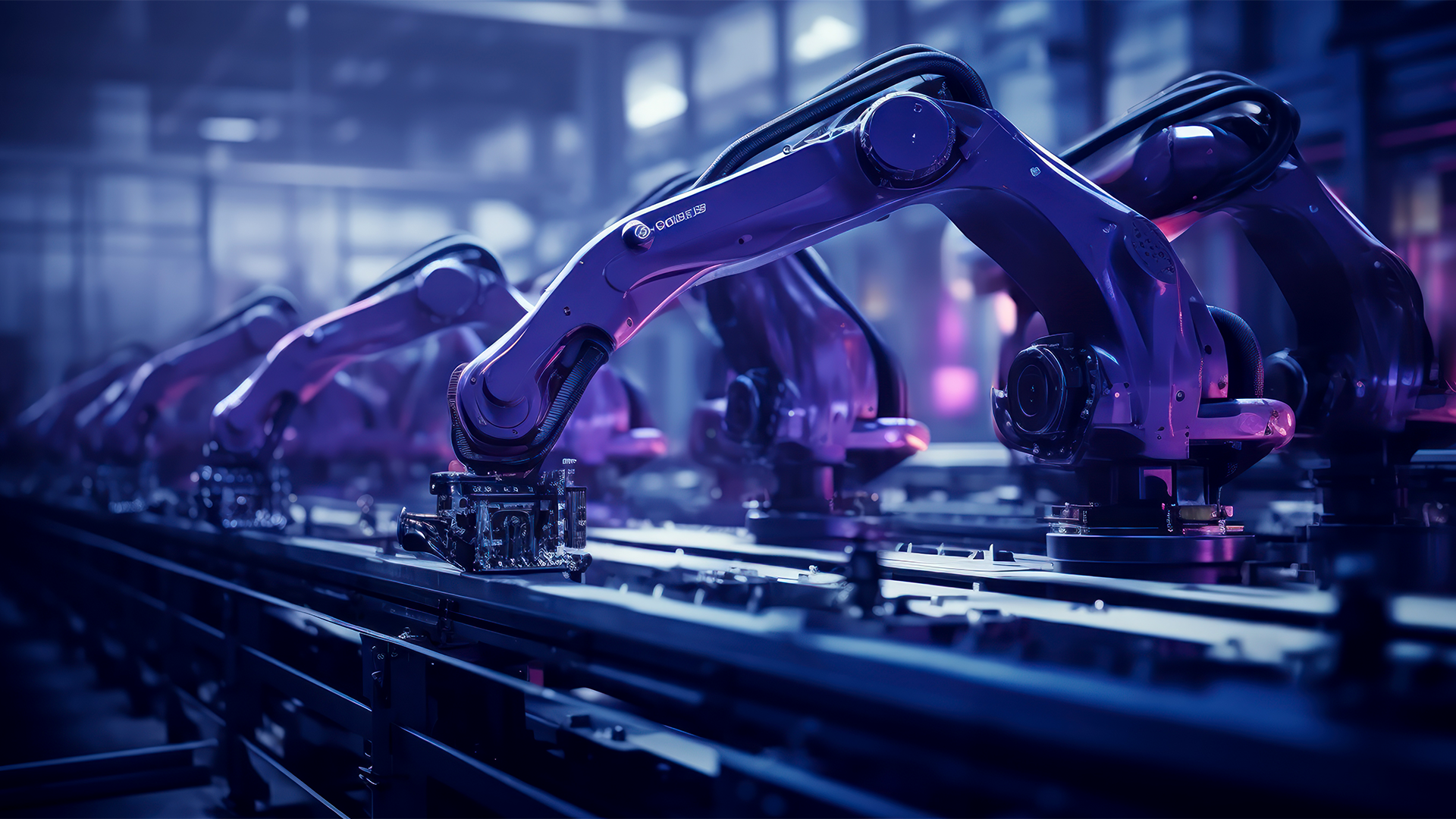
In the age of industrial automation, IoT security protocols have become the backbone of safe and efficient manufacturing processes. Automated factories rely heavily on connected devices, sensors, and machines that exchange massive amounts of data. However, these interconnected environments also introduce a host of cybersecurity challenges.
For manufacturers using containers to orchestrate and deploy applications, security is no longer optional—it’s essential. Combining industrial IoT security with container-based solutions ensures that manufacturers can secure their automated processes while achieving scalability and efficiency.
In this blog, we’ll explore the importance of IoT security protocols in manufacturing, their challenges, and how containers are transforming industrial cybersecurity.
IoT security protocols are rules and frameworks designed to safeguard connected devices, data exchanges, and communication networks in an IoT ecosystem. These protocols ensure:
Secure authentication of IoT devices.
Encrypted data transmission.
Access control for authorised users only.
In automated manufacturing, where IoT sensors and devices are integral, protocols like MQTT (Message Queuing Telemetry Transport), CoAP (Constrained Application Protocol), and DTLS (Datagram Transport Layer Security) provide essential layers of protection.
Containers, lightweight and portable, are widely used in industrial automation for deploying applications and managing IoT devices. Their ability to isolate processes and secure runtime environments makes them an ideal choice for industrial IoT ecosystems.
Key Benefits of Containers in IoT Security:
Isolation: Containers isolate applications from each other, minimising the risk of cross-contamination in case of a breach.
Scalability: Containers allow manufacturers to scale IoT operations rapidly without compromising security.
Consistency: By deploying applications in containers, organisations ensure uniform security configurations across all devices.

Automated manufacturing environments face unique industrial IoT security challenges:
Device Authentication: Ensuring that only authorised IoT devices can access the network is critical to prevent unauthorised breaches.
Data Transmission Security: Sensitive data exchanged between IoT sensors and central systems must be encrypted to prevent interception.
IoT Vulnerability Management: Many IoT devices lack the capability for regular updates, making them vulnerable to exploitation.
Container Orchestration Security: Platforms like Kubernetes used to manage containerised IoT applications need robust configurations to prevent attacks.
Industrial Control System Security: Critical systems like SCADA (Supervisory Control and Data Acquisition) must be shielded from cyberattacks targeting operational disruptions.
2. CoAP
Designed for resource-constrained devices in IoT ecosystems.
Uses DTLS to ensure secure data transmission.
3. DTLS
Extends TLS security to datagram protocols like UDP, ensuring fast and secure communication for IoT devices.
4. OPC UA (Open Platform Communications Unified Architecture)
A protocol designed for industrial automation.
Provides encryption, authentication, and authorisation mechanisms.
5. IEEE 802.1X
Secures network access through port-based authentication, ensuring only authorised devices connect to the IoT ecosystem.
Image Scanning: Ensure container images are free from vulnerabilities before deployment.
Runtime Monitoring: Use tools to monitor container activity and detect unusual behaviour in real-time.
Access Control: Limit access to container orchestration tools like Kubernetes.
Network Policies: Apply micro-segmentation to restrict communication between containers.
Automated Updates: Regularly patch container images to address emerging vulnerabilities.

1. Enhanced Device Authentication
Containers support secure protocols that validate the identity of IoT devices, preventing unauthorised access to networks.
2. Simplified Compliance
By maintaining consistent security configurations across devices, containers help meet compliance requirements for data security in industrial environments.
3. Rapid Threat Mitigation
Containers can be restarted or replaced instantly, reducing downtime and mitigating threats in real-time.
4. Integrated Monitoring
Container-based IoT applications allow centralised monitoring of all devices and systems, ensuring quick identification of anomalies.

1. Implement Zero-Trust Security Models
Adopt a zero-trust approach where every IoT device and application must be authenticated before accessing resources.
2. Encrypt All Communications
Ensure that all data exchanged within the IoT ecosystem is encrypted using protocols like TLS or DTLS.
3. Regularly Update Firmware and Applications
Keep IoT device firmware and container images up to date to mitigate vulnerabilities.
4. Conduct Regular Security Audits
Audit your IoT environment and container configurations to identify and address security gaps.
5. Leverage DevSecOps Practices
Integrate security into the development and deployment lifecycle of IoT applications.
To address IoT security protocols in automated manufacturing with containers, the following Microminder CS services can be instrumental:
1. IoT Security Assessment Services
How It Helps: Evaluates vulnerabilities in IoT ecosystems, including devices, networks, and communication protocols like MQTT or CoAP.
Benefits: Identifies security gaps in IoT infrastructure and offers actionable solutions to mitigate risks.
2. Container Security Solutions
How It Helps: Secures containerised applications used in IoT systems with features like image scanning, runtime monitoring, and access control.
Benefits: Ensures that container orchestration platforms like Kubernetes and Docker are properly configured and monitored.
3. Vulnerability Management Services
How It Helps: Continuously scans IoT devices, firmware, and containerised applications for vulnerabilities and provides patch management solutions.
Benefits: Keeps the manufacturing ecosystem resilient against emerging threats.
4. Threat Detection and Response Services
How It Helps: Provides real-time monitoring of IoT systems and containers for abnormal behaviour or security breaches.
Benefits: Enables rapid identification and response to cyberattacks, minimising downtime and operational impact.
5. Industrial Control System (ICS) Security
How It Helps: Protects critical industrial control systems like SCADA that manage automated manufacturing processes.
Benefits: Prevents disruptions to production lines by securing ICS against cyber threats.
6. Security Architecture Review Services
How It Helps: Assesses the overall security design of IoT and containerised environments in automated manufacturing.
Benefits: Ensures that security measures align with industry best practices and compliance standards.
7. DevSecOps Services
How It Helps: Integrates security into the development lifecycle of IoT applications and containerised solutions.
Benefits: Ensures that security is prioritised from the early stages of IoT and application development.
8. Cloud Security Solutions
How It Helps: Secures cloud infrastructure hosting containerised applications and IoT device management platforms.
Benefits: Provides data encryption, access control, and compliance support for cloud-native IoT systems.
9. Incident Response Services
How It Helps: Offers rapid support in the event of a security breach in IoT or containerised environments.
Benefits: Minimises damage, ensures continuity, and provides forensic analysis to prevent recurrence.
10. Managed Security Services
How It Helps: Provides 24/7 monitoring and management of IoT security, container environments, and industrial networks.
Benefits: Reduces the burden on internal IT teams and ensures a proactive security approach.
By leveraging these services, organisations in automated manufacturing can secure their IoT environments, containerised applications, and industrial control systems against evolving threats. This ensures operational resilience, compliance, and long-term growth.
The integration of IoT security protocols with container-based solutions offers manufacturers in Saudi Arabia a robust approach to securing automated environments. From protecting sensitive data to preventing operational disruptions, these strategies ensure that industrial automation evolves without compromising security.
As the manufacturing industry continues to embrace digital transformation, adopting advanced security measures will not only protect critical infrastructure but also drive long-term business resilience.
Are you ready to transform your IoT security strategy? Advanced container-based solutions and IoT protocols can secure your automated manufacturing processes, ensuring both safety and efficiency. Let’s discuss how to tailor these solutions to your needs. Reach out today!
Don’t Let Cyber Attacks Ruin Your Business
Call
UK: +44 (0)20 3336 7200
KSA: +966 1351 81844
UAE: +971 454 01252
Contents
To keep up with innovation in IT & OT security, subscribe to our newsletter
Recent Posts
Penetration Testing | 10/11/2025
Cloud Security | 07/11/2025
Cybersecurity | 06/11/2025
What are IoT security protocols?
IoT security protocols are frameworks and rules that protect IoT devices and their communication networks. They ensure secure authentication, encryption, and data transfer between connected devices.Why is IoT security important in automated manufacturing?
Automated manufacturing relies on IoT devices to control operations, monitor performance, and optimise workflows. Without robust security, these systems are vulnerable to data breaches, operational disruptions, and cyberattacks.What are the common IoT security threats in manufacturing?
Unauthorised access to IoT devices. Malware targeting IoT sensors. Data breaches during device communication. Vulnerabilities in outdated firmware or software. Distributed Denial of Service (DDoS) attacks on IoT networks.How do containers enhance IoT security?
Containers isolate applications, making it harder for a breach in one component to affect the entire system. They also support consistent security configurations and are easier to update and patch.What are the best practices for securing IoT in manufacturing?
Use strong authentication for IoT devices. Encrypt all data transmissions. Regularly update device firmware and software. Monitor network traffic for anomalies. Conduct regular security audits and vulnerability assessments.